http://www.politico.com/story/2014/01/cyberattack-federal-courts-102594.html
( Is anything secure ? )

http://www.zerohedge.com/news/2014-01-23/hacked-cnn-reports-china-dumps-all-us-bonds
( Is anything secure ? )
Court system hit with cyberattack

Unidentified hackers took aim at the federal court system Friday, blocking access to its public website while preventing lawyers and litigants from filing legal documents online.
The incident affected uscourts.gov, the federal court’s public hub, as well as most if not all federal court sites — not to mention the federal court system’s electronic filing system and its access page, PACER, a spokesman for the Administrative Office of the U.S. Courts said Friday.
The aide described the incident only as a denial-of-service attack, and that the court system, which manages its own cybersecurity, is still investigating the exact nature of the incident and who’s responsible.
Earlier Friday, a federal court clerk from Arkansas indicated in an email obtained by POLITICO that it appeared to be a “new national cyberattack on the judiciary,” but he did not provide any additional information about the type of attack or who might be behind it.
The Justice Department, for its part, did not comment for this story. The Department of Homeland Security, which plays a key role monitoring federal networks and disseminating information about cyber threats, could not be reached for comment.
http://www.zerohedge.com/news/2014-01-23/hacked-cnn-reports-china-dumps-all-us-bonds
Hacked CNN Reports "China Dumps All US Bonds"
Submitted by Tyler Durden on 01/23/2014 20:20 -0500







 The issue came to light on the company’s support forum after camera experts discovered that the Web interface for many Foscam cameras can be accessed simply by pressing “OK” in the dialog box when prompted for a username and password. Reached via email, the company’s tech support division confirmed that the bug exists in MJPEGcameras running .54 version of the company’s firmware.
The issue came to light on the company’s support forum after camera experts discovered that the Web interface for many Foscam cameras can be accessed simply by pressing “OK” in the dialog box when prompted for a username and password. Reached via email, the company’s tech support division confirmed that the bug exists in MJPEGcameras running .54 version of the company’s firmware.









It's one thing for the Comedy News Network formerly known as CNN to announce the opposite verdict on Obamacare as breaking news or that the TV studio formerly known as the NYSE is under 3 feet of water (based on what it saw on Twitter). It's something else entirely for it to report that China has declared semi-hot war on the US (unless of course CNN is merely reporting tomorrow's news today).
This is a cached version of a CNN website that appeared one short hour ago.
Luckily this time it was merely a a hack, as can be seen by the "article's" subsequent deletion from the live page and as CNN reported subsequently:
- CNN SAYS SOME OF ITS SOCIAL MEDIAL ACCOUNTS WERE COMPROMISED
- CNN SAYS COMPROMISED ACCOUNTS INCLUDE TWITTER PAGE, FACEBOOK
But perhaps more telling is the complete lack of market response to even the hacked article, so different to the AP hack from last summer. Just goes to show how irrelevant the once upon a time only news network has become.
h/t @rosswernej
Bug Exposes IP Cameras, Baby Monitors
A bug in the software that powers a broad array of Webcams, IP surveillance cameras and baby monitors made by Chinese camera giant Foscam allows anyone with access to the device’s Internet address to view live and recorded video footage, KrebsOnSecurity has learned.
 The issue came to light on the company’s support forum after camera experts discovered that the Web interface for many Foscam cameras can be accessed simply by pressing “OK” in the dialog box when prompted for a username and password. Reached via email, the company’s tech support division confirmed that the bug exists in MJPEGcameras running .54 version of the company’s firmware.
The issue came to light on the company’s support forum after camera experts discovered that the Web interface for many Foscam cameras can be accessed simply by pressing “OK” in the dialog box when prompted for a username and password. Reached via email, the company’s tech support division confirmed that the bug exists in MJPEGcameras running .54 version of the company’s firmware.
Foscam said it expects to ship an updated version of the firmware (Ver. 55) that fixes the bug by Jan. 25. The new firmware will be published on the company’s website. According to Foscam, the problem affects the following models: FI8904W, FI8905E, FI8905W, FI8906W, FI8907W, FI8909W, FI8910E, FI8910W, FI8916W, FI8918W, and FI8919W. Foscam users can determine if their camera is affected by following the instructions here.
Don Kennedy, a camera enthusiast and active member of the Foscam support forum who helped to diagnose and report the firmware problem, also posted a workaround for the bug until Foscam issues an official fix. Kennedy said the vulnerability comes on the heels of another Foscam flaw that drew widespread media attention in August 2013, in which some creep reportedly used a similar vulnerability to shout obscenities at a sleeping toddler.
This is just the latest in a string of such discoveries. In 2012, researchers revealed that a large number of IP cameras made by TRENDnet were similarly vulnerable to snooping by outsiders. While these types of vulnerabilities require outsiders to know the exact Internet address of vulnerable cameras, specialized search engines like SHODAN can be used to pinpoint devices that may not be indexed by typical search engines.
Gang Rigged Pumps With Bluetooth Skimmers
Authorities in New York on Tuesday announced the indictment of thirteen men accused of running a multi-million dollar fraud ring that allegedly installed Bluetooth-enabled wireless gas pump skimmers at filling stations throughout the southern United States.
According to documents released by Manhattan District Attorney Cyrus R. Vance, Jr., the accused stole more than $2.1 million in the scheme. Investigators say the men somehow gained access to pumps at Raceway and Racetrac gas stations throughout Georgia, South Carolina and Texas and installed skimming devices like the one pictured below.

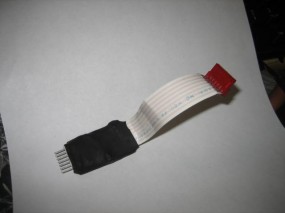
A Bluetooth enabled gas pump skimmer lets thieves retrieve stolen card and PIN data wirelessly while they gas up. Image: Manhattan DA.
These devices connect directly to the pump’s power supply, and include a Bluetooth chip that enables thieves to retrieve the stolen data wirelessly — just by pulling up to the pump and opening up a laptop. The defendants allegedly then encoded the stolen card data onto counterfeit cards, and armed with stolen PINs withdrew funds from victim accounts at ATMs. The defendants then allegedly deposited the funds into accounts in New York that they controlled, after which co-conspirators in California and Nevada would withdraw the cash in sub-$10,000 increments to avoid triggering anti-money laundering reporting requirements by the banks.
This blog has featured several stories about gas-pump skimmers that were Bluetooth enabled. What’s remarkable is how common these attacks have become (Google Newsand Twitter are full of local news reports of apparent gas pump skimmer attacks, like this one at a Pilot station in Tennessee last week).
Last year, I received some information from a police officer in California who is tasked with chronicling many of these incidents (this seems to have become something of a full-time job for him). He sent me some pictures of a few several more common gas pump skimmers that show up at filling stations in his state, including the devices show above right and below left.
The incident reports he filed on the devices pictured below indicates that thieves involved in this type of crime have a typical playbook. These crimes, as with attacks on regular bank ATMs, tend to occur on weekends, often in the early morning hours. From his report:
“M.O.: Two or three suspects exit vehicle, look around for people watching them, then pretend to pump gas by placing the dispenser into the gas tank. One suspect will eventually enter the store, pay cash to purchase a small amount of gas or a drink to distract attention away from the pump. Meanwhile, another suspect places a skimming device inside the pump by opening the front with a universal key. Time to install/remove is between 5 – 10 minutes.”
I don’t worry too much about gas pump skimmers; there is virtually no way for the average consumer to tell if a pump has been compromised. But I would urge readers to avoid paying at the pump using a debit card. While debit cards have the same zero-liability protection afforded to credit cards, having your checking account emptied of cash can be a huge hassle and create secondary problems (bounced checks, for instance).

Gas pump skimmers recovered by police in California.
More information about the indictments in the New York case can be found in this press announcement (PDF).


No comments:
Post a Comment