http://www.vox.com/2014/8/21/6053819/white-house-cybersecurity-czar-brags-about-his-lack-of-technical
Michael Daniel is the White House's cybersecurity coordinator, the man who "leads the interagency development of national cybersecurity strategy and policy" for the president. And in a recent interviewwith GovInfoSecurity, he argued that his lack of technical expertise gave him an advantage in doing that job.
/cdn3.vox-cdn.com/uploads/chorus_asset/file/665960/j.michaeldaniel-cropped.0.jpg)
White House cybersecurity czar Michael Daniel (White House)
"You don't have to be a coder in order to really do well in this position," Daniel said, when asked if his job required knowledge of the technology behind information security. "In fact, actually, I think being too down in the weeds at the technical level could actually be a little bit of a distraction."
"You can get taken up and enamored with the very detailed aspects of some of the technical solutions," he explained, arguing that "the real issue is looking at the broad strategic picture."
As Princeton computer scientist (and, full disclosure, my former advisor) Ed Felten points out, it's hard to imagine senior policymakers with responsibility for other technical subjects making this kind of claim. Imagine a White House economic advisor arguing that experience in the weeds of economic research would be a distraction, an attorney general making that claim about time in a courtroom, or a surgeon general bragging about never having set foot in an operating room.
****
http://www.businessinsider.com/51-ups-stores-targeted-by-hackers-2014-8
UPS: Some Of Our Stores Were Hacked
The United States Postal Service said on Wednesday that 51 of its UPS Store locations were targeted by hackers in an attack that spread across 24 states in the U.S. That's about 1% of its locations in the U.S.
Any customers who used a credit or debit card in UPS stores between Jan. 20 and Aug. 11 may have been exposed to the malware, which was found on the company's servers in the 51 franchise stores, The Financial Times reported. Names, postal addresses, email addresses, and card information are thought to be among the data that may have been exposed to hackers, UPS said in a statement.
The U.S. Department for Homeland Security contacted UPS to inform them of the data breach, and the company claimed that other retailers were also notified of the spread of a new type of malware being used to target U.S. retail locations. According to UPS, the malware was removed from systems on Aug. 11. Stores are now safe to shop in.
****
http://krebsonsecurity.com/2014/08/counterfeit-u-s-cash-floods-crime-forums/
Counterfeit U.S. Cash Floods Crime Forums
One can find almost anything for sale online, particularly in some of the darker corners of the Web and on the myriad cybercrime forums. These sites sell everything from stolen credit cards and identities to hot merchandise, but until very recently one illicit good I had never seen for sale on the forums was counterfeit U.S. currency.
That changed in the past month with the appearance on several top crime boards of a new fraudster who goes by the hacker alias “MrMouse.” This individual sells counterfeit $20s, $50s and $100s, and claims that his funny money will pass most of the tests that merchants use to tell bogus bills from the real thing.
MrMouse markets his fake funds as “Disney Dollars,” and in addition to blanketing some of the top crime forums with Flash-based ads for his service he has boldly paid for a Redditstickied post in the official Disney Market Place.
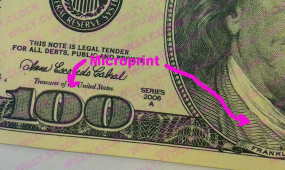
Judging from images of his bogus bills, the fake $100 is a copy of the Series 1996 version of the note — not the most recent $100 design released by the U.S. Treasury Department in October 2013. Customers who’ve purchased his goods say the $20 notes feel a bit waxy, but that the $50s and $100s are quite good fakes.
MrMouse says his single-ply bills do not have magnetic ink, and so they won’t pass machines designed to look for the presence of this feature. However, this fraudster claims his $100 bill includes most of the other security features that store clerks and cashiers will look for to detect funny money, including the watermark, the pen test, and the security strip.
****
http://krebsonsecurity.com/2014/08/why-so-many-card-breaches-a-qa/
Why So Many Card Breaches? A Q&A
The news wires today are buzzing with stories about another potentially major credit/debit card breach at yet another retail chain: This time, the apparent victim is AB Acquisition, which operates Albertsons stores under a number of brands, including ACME Markets, Jewel-Osco, Shaw’s and Star Markets. Today’s post includes no special insight into this particular retail breach, but rather seeks to offer answers to some common questions regarding why we keep hearing about them.
Credit and debit cards stolen from bricks-and-mortar stores (called “dumps”) usually sell for at least ten times the price of cards stolen from online merchants (referred to in the underground as “CVVs” or just “credit cards”). As a result, dumps are highly prized by today’s cyber crooks, and there are dozens of underground “card shops” online that will happily buy the cards from hackers and resell them on the open market. For a closer look at how these shops work (and how, for example, the people responsible for these retail break-ins very often also are actually running the card shops themselves) see Peek Inside a Carding Shop.
Okay, I’ll bite: Why are dumps so much more expensive and valuable to attackers?
A big part of the price difference has to do with the number of steps it takes for the people buying these stolen cards (a.k.a. “carders”) to “cash out” or gain value from the stolen cards. For example, which of these processes is likely to be more successful, hassle-free and lucrative for the bad guy?
1. Armed with a stack of dumps, a carder walks into a big box store and walks out with high-priced electronics or gift cards that he can easily turn into cash.
2. Armed with a list of CVVs, a carder searches online for stores that will ship to an address that is different from the one on the card. Assuming the transaction is approved, he has the goods shipped to a guy he knows at another address who will take a cut of the action. That is, *if* the fraudulently purchased goods don’t get stopped or intercepted along the way by the merchant or shipping company when someone complains about a fraudulent transaction.
If you guessed #1, you’re already thinking like a carder!
Snap! But it seems like these breaches are becoming more common. Is that true?
It’s always hard to say whether something is becoming more common, or if we’re just becoming more aware of the thing in question. I think it’s safe to say that more people are looking for patterns that reveal these retail breaches (including yours truly, but somehow this one caught me– and just about everyone I’ve asked — unawares).
Certainly, banks — which shoulder much of the immediate cost from such breaches — are out for blood and seem more willing than ever to dig deep into their own fraud data for patterns that would reveal which merchants got hacked. Visa and MasterCard each have systems in place for the banks to recover at least a portion of the costs associated with retail credit and debit card fraud (such as the cost of re-issuing compromised cards), but the banks still need to be able to tie specific compromised cards to specific merchant breaches.
****

No comments:
Post a Comment