Some blues you can use .....
http://abcnews.go.com/blogs/technology/2014/06/solar-flares-disrupt-communications-on-earth-could-send-shockwave-on-friday-the-13th/
Solar Flares Disrupt Communications on Earth, Could Send Shockwave on Friday the 13th
Jun 11, 2014 4:34pm
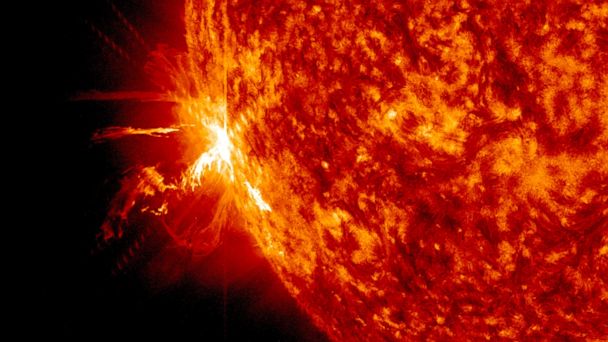
A solar flare erupts on the surface of the sun, June 10, 2014. (Goddard/SDO/NASA)
The sun has had three major solar flares on its surface in the past two days that have affected communications on Earth and could send a shockwave through Earth this Friday, according to the National Oceanic and Atmospheric Administration.
The “solar events” caused brief blackouts in high frequency communications when they struck, twice on Tuesday morning and once this morning, all between the hours of 7 a.m. and 9 a.m. EDT.
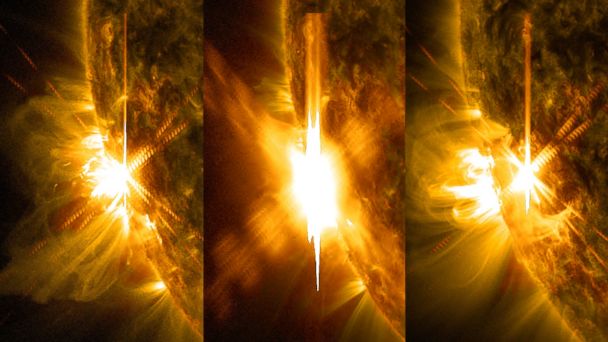
Three X-class flares erupted from the left side of the sun; the first two from left occurred June 10, 2014, and the last occurred June 11, 2014. (Goddard/SDO/NASA)
Solar flares are bursts of radiation on the sun’s surface. The disturbance to Earth’s atmosphere can disrupt GPS and communications signals, according to NASA.
One of the flares created a “coronal mass ejection” that actually could come into contact with Earth on Friday, according to NOAA. The ejection is essentially a huge cloud of plasma that could hit the Earth and cause a shock wave, affecting communications systems. If an ejection were to hit Earth on Friday, scientists expect it would only cause a minor geo-magnetic storm, according to NOAA.
The flares were observed by NASA, which posted stunning photos and videos of the events on its website.
http://spaceweather.com/
ANOTHER X-FLARE: Solar activity remains high. Active sunspot AR2087 unleashed another X-flare on June 11th (X1.0), following two X-flares (X2.1 and X1.5) on June 10th. The latest blast was intense but short-lived, and it is not expected to have significant Earth-effects. Solar flare alerts: text, voice
INCOMING CME: Yesterday's double X-flare may have produced a geoeffective CME after all. At first it appeared that Earth was outside the line of fire, but a closer look at the CME reveals an Earth-directed component. Click to view a movie of the explosion from the Solar and Heliospheric Observatory:
The movie shows a faint CME associated with the first X-flare emerging around 1200 UT. A second, brighter CME from the second X-flare quickly overtakes it, forming a "cannibal CME." Computer models run yesterday by NOAA analysts suggest the merged storm cloud will reach Earth mid-day on June 13th. The glancing blow could spark polar geomagnetic storms.
Meanwhile, more X-flares are in the offing. At least two sunspots (AR2080 and AR2087) have unstable 'delta-class' magnetic fields that could erupt at any moment. The source of yesterday's X-flares, AR2087, is particularly potent, and it is turning toward Earth. NOAA forecasters estimate a 60% chance of M-flares and a 30% chance of X-flares on June 11th. Solar flare alerts: text, voice
Just a coincidence ? Meaning the timing ........
http://news.sky.com/story/1274201/cyber-attack-to-hit-in-next-two-weeks
Cyber Attack 'To Hit In Next Two Weeks'
Up to a million computers have already been infected by software that steals bank details and demands a ransom.

Video: The Battle To Disrupt Cyber Attack
Enlarge
The UK boss of Samsung on how technology is shaping our economy, that threat of a "colossal" cyber attack and competing with arch-rival Apple.
Video: UK Samsung Boss On Cyber Attack
Enlarge
Computer users are being urged to protect their machines from malware which allows hackers to steal financial data.
British investigators have been working with the FBI to trace the hackers behind ongoing attacks, and the botnet system used by the targets has been temporarily disrupted.
But the UK's National Crime Agency says people have just two weeks before the system could be functioning again, and urged people to protect their computers from an expected "powerful computer attack".

Between 500,000 and one million machines have so far been infected worldwide, according to court documents.
US officials have accused a Russian hacker of masterminding the scam - and prosecutors say those involved have already raked in more than $100m (£60m).
The NCA is urging people to back up important files and make sure their security software and operating system are up to date.
Two pieces of malware software known as GOZeuS and CryptoLocker are responsible for the alert.
They typically infect a computer via attachments or links in emails.
If a user clicks on GOZeuS, it silently monitors activity and tries to capture information such as bank details.
"(The links or attachments) may look like they have been sent by genuine contacts and may purport to carry invoices, voicemail messages, or any file made to look innocuous," the NCA warned.
"These emails are generated by other victims' computers, who do not realise they are infected, and are used to send mass emails creating more victims."
The Cryptolocker malware is activated if the first attack is not profitable enough.
It locks a user from their files and threatens to delete them unless a "ransom" of several hundred pounds is paid.
Some 234,000 machines were hit by Cryptolocker - bringing in $27m (£16m) in payments - in its first two months, the US Justice Department said.

More than 15,500 computers in the UK are infected and "many more" are at risk, according to the NCA.
Stewart Garrick, a senior investigator with the NCA, told Sky News the threat was mainly against individuals or businesses running Windows-based computers.
Thirty-year-old Russian Evgeniy Bogachev is the alleged leader of the gang behind the attacks, FBI executive assistant director Robert Anderson told a news conference in Washington DC.
US and other agents seized servers around the world this weekend and freed 300,000 computers from the infection.
"They (the FBI) have disrupted the network and taken control of it," said Sky's Tom Cheshire.
"So when the hackers try to speak to the computer that's affected, that line of communication has been cut off.
"You now have a chance to clean up. The first thing you should do is update your operating system - especially if you're on Windows, then look to scan your computer for viruses and it should be able to find it."
and......
Russia Today........
2 weeks to prepare for 'powerful' virus strike-back in major malware offensive
The UK has warned its computer-users they have two weeks to protect their machines from two powerful viruses, GameOver Zeus and Cryptolocker, after a US-led multinational operation announced a coordinated takedown of malware.
There are more than 15,500 computers infected in the UK and many more are at risk, the UK’s National Crime Agency has said, citing “intelligence” assumptions.
It “could cost computer users millions of pounds,” the NCA warned.
The agency is now “urging the public and small businesses” to consult with the government-backed getsafeonline.org website.
“Nobody wants their personal financial details, business information or photographs of loved ones to be stolen or held to ransom by criminals. By making use of this two-week window, huge numbers of people in the UK can stop that from happening to them,” Deputy Director of the NCA’s Cyber Crime Unit Andy Archibald said.
However, computer users need to take action immediately, as authorities only have temporary control of communications.
"This warning is not intended to cause you panic but we cannot over-stress the importance of taking these steps immediately. This is because the UK's NCA has taken temporary control of the communications used to connect with infected computers, but expects only a very limited window of opportunity to ensure you are protected," said UK-based Get Safe Online, a government-backed organization that has published a list of software it recommends for the task.
With the warning reaching the public, Get Safe’s website crashed under the number of requests to view its content.
The organization’s Chief Executive Tony Neate insisted that this was not due to a cyber-attack.
The NCA’s warning relates to a strain of malware known as Cryptolocker, which works together with another malware, Gameover Zeus (also known as GOZeus or P2PZeus).
GOZeus is usually downloaded by unsuspecting users in what is known as a phishing attack, often in the form of an email which looks legitimate, but which is in fact designed to trick someone into downloading malicious software.
Once inside someone’s machine, the malware then searches for files containing financial information. If it cannot find anything, it will install Cryptolocker, which locks the computer until a ransom fee is paid.
According to the US-led team of investigators, which include FBI, NCA, and Europol, Gameover Zeus virus estimate that between 500,000 and 1 million computers around the world. A quarter of victims are said to be the US, where computer-users have lost more than $100 million to Gameover Zeus.
Cryptolocker alone infected more than 234,000 machines and won $27 million in ransom payments in just its first two months, the Justice Department said.
In the biggest operation of its kind, servers all over the world were raided simultaneously by the NCA, FBI, Europol, and other authorities.
This meant police could direct what are known as Command and Control (C&C) servers, which hackers and criminals use to control the operation of the botnet. A botnet is a network of home computers often controlled by a criminal gang.
“The scale of this operation is unprecedented. This is the first time we’ve seen a coordinated international approach of this magnitude, demonstrating how seriously the FBI takes this current threat,” Steve Rawlinson from Tagadab, a web-hosting company involved in the bust, told the BBC.
The FBI accuses a Russian called Evgeny Bogachev, who they have identified a ringleader of the gang. Bogachev, 30, is now facing 14 criminal charges alleging that he is the “administrator” of GameOver Zeus. He is also accused of being a leader of the “tightly-knit gang” behind CyberLocker.
 Email
Email

Good morning, unbelievable amount of "stories" going on, Iraq jumping to the front was a surprise to me. Really getting hard to keep up with things, guess my next car should be one that gets good gas mileage.
ReplyDeleteYou guys have a good one.
crazy days and nights !
ReplyDelete