Published on Friday, May 9, 2014 by Common Dreams
Obama Directive Makes Mere Citing of Snowden Leaks
Offense
Once promising the most transparent administration in history, White House reins in free speech of employees
 Directive from the Office of the Director of National Intelligence (ODNI) makes mention of news reporting referencing unauthorized informatin, like that leaked by NSA whistleblower Edward Snowden, a punishable offense. (Image credit: Laura Poitras)In a new policy directive from the Obama administrative, national security and other government officials will no longer be allowed to publicly discuss or even reference news reporting that is based on "unauthorized leaks."
Directive from the Office of the Director of National Intelligence (ODNI) makes mention of news reporting referencing unauthorized informatin, like that leaked by NSA whistleblower Edward Snowden, a punishable offense. (Image credit: Laura Poitras)In a new policy directive from the Obama administrative, national security and other government officials will no longer be allowed to publicly discuss or even reference news reporting that is based on "unauthorized leaks."
President Obama once promised the American people that his administration would be the most transparent in history, but after years of fights with civil libertarians trying to obtain legal memos used to justify the president's overseas assassination program, an unprecedented pattern of prosecuting government whistleblowers, the targeting of journalists, and all the secrecy and obfuscation related to the NSA's mass surviellance programs made public by Edward Snowden, that claim is now met with near universal laughter, if not scorn, by critics.
According to the New York Times:
A new pre-publication review policy for the Office of Director of National Intelligence says the agency’s current and former employees and contractors may not cite news reports based on leaks in their speeches, opinion articles, books, term papers or other unofficial writings.Such officials “must not use sourcing that comes from known leaks, or unauthorized disclosures of sensitive information,” it says. “The use of such information in a publication can confirm the validity of an unauthorized disclosure and cause further harm to national security.”Failure to comply “may result in the imposition of civil and administrative penalties, and may result in the loss of security clearances and accesses,” it says.
Timothy H. Edgar, a visiting professor at Brown University, told the Times the ODNI directive is overly restrictive because it goes beyond telling officials they cannot comment on or confirm the accuracy of unauthorized leaks—something he thinks makes sense and is already covered by statute—but it bizarrely asserts that these people cannot even acknowledge the existence of a story that may have appeared on the cover of a major newspaper.
“You’re basically saying people can’t talk about what everyone in the country is talking about,” Edgar said. “I think that is awkward and overly broad in terms of restricting speech.”
The new rule was first reported by journalist Steve Aftergood at the Secrecy News website on Thursday and relates to other rules that guide national security officials who are speak to the press or in public forums.
Referencing the Times reporting on the directive, the president's critics were focused on the continued hypocrisy between claims of transparency by the president and other high-level officials and the reality represented by the continued attempt to by the White House and Director of National Intelligence James Clapper to control information:





Aloha,
ReplyDeleteThe committee to eliminate the unauthorized leakage info ,,, code name -- "Team Depends",, Sorry, couldn't resist.
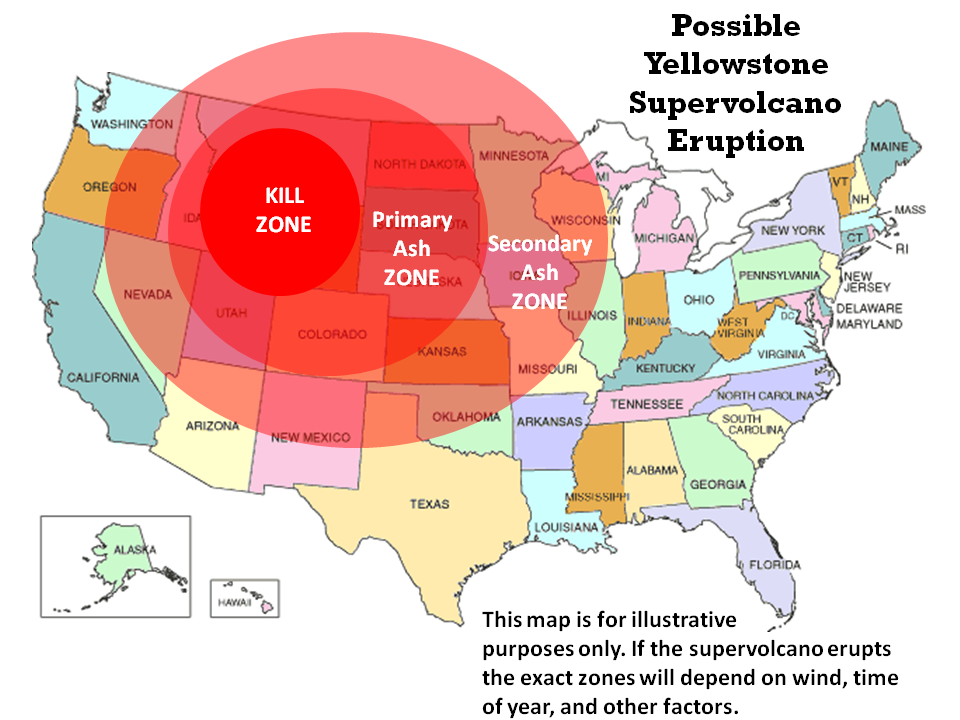
Interesting article about the Yellowstone evac probabilities , 'ere's one anout refusing to focus on real events being ignored from AJ's site :
http://www.prisonplanet.com/selective-climate-alarmism-of-white-house-ignores-imminent-threats-of-emp-attack-debt-collapse-and-fukushima-catastrophe.html
On that note, this audio clip from last June with JHK and WT made an interesting point. http://kunstler.com/podcast/kunstlercast-235-talking-to-petroleum-geologist-jeffrey-brown/
In the interview ,WT was talking about after the crash,there may be "pockets of rational thinking" of people who survive. I've been wondering ever since if any of those pockets could be possible in the N hemisphere whith all the Fukushima fallout already happening and then all the rest of the Nuke plants that would be in uncontrollable status. All in all in would be quite complex to pre-determine where those 'pockets' may indeed be and situate someone from you gene pool to be included in the next round of human evOlution,eh ? I don't think strategic relocation plans have ever been more omplex then they are right now.
Somthing to ponder...or not.
NW
NW
Good evening NW ! Definitely something to ponder......What I found interesting about the Yellowstone article was on the record comments from a South African Official - of course it hasn't been officially denied yet !
Delete