Something else to ponder.......
http://rt.com/usa/retailers-hacker-attack-russian-750/
http://krebsonsecurity.com/2014/01/a-first-look-at-the-target-intrusion-malware/







 That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.
That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.







 As is the case with many data breaches, the attackers in this attack used a virtual toolbox of crimeware to get the job done. As I noted in a Tweet shortly after filing my story Wednesday, at least one of those malware samples includes the text string “Rescator.” Loyal readers of this blog will probably find this name familiar. That’s because Rescator was the subject of a blog post that I published on Dec. 24, 2013, titled “Who is Selling Cards from Target?“.
As is the case with many data breaches, the attackers in this attack used a virtual toolbox of crimeware to get the job done. As I noted in a Tweet shortly after filing my story Wednesday, at least one of those malware samples includes the text string “Rescator.” Loyal readers of this blog will probably find this name familiar. That’s because Rescator was the subject of a blog post that I published on Dec. 24, 2013, titled “Who is Selling Cards from Target?“.
![A private message on cpro[dot]su between Rescator and a member interested in his card shop. Notice the ad for Rescator's email flood service at the bottom.](http://krebsonsecurity.com/wp-content/uploads/2013/12/rescator-pm-cpro-600x153.png)
| Was "Metadata" leaked in the Target breach? | Posted by Sean @ 13:43 GMT |
The Target data breach has been big news ever since Brian Krebs broke the story several weeks ago.
And our analysts have been investigating the related malware samples, all very interesting, but one thing I'd like to know is this: if Target knows you're pregnant… do the hackers now know, too?
Back in February of 2012, the New York Times published an article by Charles Duhigg based on his book, The Power of Habit. And one of the more interesting things revealed in the article, was that Target very actively analyzes customer behavior patterns.


In other words: Target generates lots of metadata and customer analytics.
According to Bloomberg, Target has said the theft of customer data may have affected anyone who provided it basic information over the past several years. Provided?
As in data that was filled out on an application for credit — or does "provided" include data that was learned based on shopping patterns? The breach of 70 million records which included name and home address hints at a back end compromise that is far deeper than point of sale malware.
We've all learned the value of metadata in the last half-year.
Forget about the breached credit card numbers. Target's analytics would be an identity theft goldmine.
Post by — @Sean
And our analysts have been investigating the related malware samples, all very interesting, but one thing I'd like to know is this: if Target knows you're pregnant… do the hackers now know, too?
Back in February of 2012, the New York Times published an article by Charles Duhigg based on his book, The Power of Habit. And one of the more interesting things revealed in the article, was that Target very actively analyzes customer behavior patterns.


In other words: Target generates lots of metadata and customer analytics.
According to Bloomberg, Target has said the theft of customer data may have affected anyone who provided it basic information over the past several years. Provided?
As in data that was filled out on an application for credit — or does "provided" include data that was learned based on shopping patterns? The breach of 70 million records which included name and home address hints at a back end compromise that is far deeper than point of sale malware.
We've all learned the value of metadata in the last half-year.
Forget about the breached credit card numbers. Target's analytics would be an identity theft goldmine.
Post by — @Sean
http://rt.com/usa/retailers-hacker-attack-russian-750/
Target part of a broader cyber-attack, Russian hackers allegedly involved
A US government classified memo has acknowledged that the Christmas cyber-attack on Target Corp was part of a much broader security breach of a number of US companies. The document alleges that traces of Russian language were detected in the malware.
The first results of the investigation into the holiday hacker attack against Target Corp have been summed up in a secret “Indicators for Network Defenders” memo distributed by the US government among American retailers and financial service companies.
People familiar with the document claim the situation is actually much worse than appraised earlier, the Wall Street Journal reports.
The investigators have confirmed fears that Target was not the only victim of the attack, but have refrained from identifying the other companies that suffered during the Christmas sales craze.
According to Reuters’ source, at least three other well-known national retailers have suffered an attack from the same virus.
On Thursday, luxury retailer Neiman Marcus Group said that it also suffered a theft of clients’ personal data during the holiday shopping period, without mentioning, though, whether its case was somehow related to Target's.
In an attempt to expose the plotters of the attack against Target Corp, America’s third-largest retail company, the US Department of Homeland Security’s National Cybersecurity and Communications Integration Center teamed up with Dallas-based iSight Partners, a cybersecurity company, which distributed its own version of the memo Thursday.
Russian connection?
It has been revealed that the virus used by the international hackers to breach Target’s firewall and compromise the personal data of 70 million people was dubbed by hackers KARTOKHA (“potato” in Russian) first appeared on the international hacker black market last spring.
In fact, it was just the latest virus among many to target point-of-sale (POS) terminals. The most notorious of these viruses are BlackPOS, Dexter and vSkimmer, Reuters reports.
Tiffany Jones, a senior vice president at iSight, described the method and scale of the attack as “unique.” She also noted that the malware was specifically designed to meticulously conceal its data manipulations, making the very detection of the virus in action a very hard task.
The identities of those who bought and accustomed this state-of -the-art, expensive malware program for the Target attack remain unknown. At the same time the investigators claim the source code of the virus contain certain words in Russian, most probably in the comments to the program. This might point to the fact that the source code of the virus was developed with the help of skilled Russian-speaking codeheads from the former Soviet Union.
“The intrusion operators displayed innovation and a high degree of skill,” the iSight report says.
KARTOKHA in action
The memo does not specify how the hackers managed to break into the Target’s networks, but the breach exposed the outdated security tools used in banking. The KARTOKHA virus (codenamed POSRAM Trojan by iSight programmers) could not be identified by any anti-virus software, the memo claims.
Also, it has been found that the actual hacking process was split into two stages. First, the Target Corp plastic card payment devices were infected with the virus, which made copies of personal data encrypted on magnetic stripes on payment cards and stored them on Target’s own servers. Then the hackers broke into the company’s system network to collect the stolen data.
One of the peculiarities of the virus was that it did not operate around the clock, limiting its activities to only prime business hours between 10 am and 5 pm, which also contributed to invisibility of the malware.
http://krebsonsecurity.com/2014/01/a-first-look-at-the-target-intrusion-malware/
A First Look at the Target Intrusion, Malware
Last weekend, Target finally disclosed at least one cause of the massive data breach that exposed personal and financial information on more than 110 million customers: Malicious software that infected point-of-sale systems at Target checkout counters. Today’s post includes new information about the malware apparently used in the attack, according to two sources with knowledge of the matter.
In an interview with CNBC on Jan. 12, Target CEO Gregg Steinhafel confirmed that the attackers stole card data by installing malicious software on point-of-sale (POS) devices in the checkout lines at Target stores. A report published by Reuters that same day stated that the Target breach involved memory-scraping malware.
This type of malicious software uses a technique that parses data stored briefly in the memory banks of specific POS devices; in doing so, the malware captures the data stored on the card’s magnetic stripe in the instant after it has been swiped at the terminal and is still in the system’s memory. Armed with this information, thieves can create cloned copies of the cards and use them to shop in stores for high-priced merchandise. Earlier this month, U.S. Cert issued a detailed analysis of several common memory scraping malware variants.
Target hasn’t officially released details about the POS malware involved, nor has it said exactly how the bad guys broke into their network. Since the breach, however, at least two sources with knowledge of the ongoing investigation have independently shared information about the point-of-sale malware and some of the methods allegedly used in the attack.
‘BLACK POS’
On Dec. 18, three days after Target became aware of the breach and the same day this blogbroke the story, someone uploaded a copy of the point-of-sale malware used in the Target breach to ThreatExpert.com, a malware scanning service owned by security firm Symantec. The report generated by that scan was very recently removed, but it remains available via Google cache (Update, Jan. 16, 9:29 a.m.: Sometime after this story ran, Google removed the cached ThreatExpert report; I’ve uploaded a PDF version of it here).
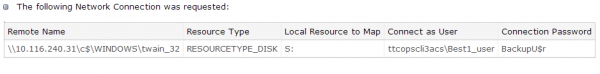
According to sources, “ttcopscli3acs” is the name of the Windows computer name/domain used by the POS malware planted at Target stores; the username that the malware used to upload stolen data data was “Best1_user”; the password was “BackupU$r”
According to a source close to the investigation, that threatexpert.com report is related to the malware analyzed at this Symantec writeup (also published Dec. 18) for a point-of-sale malware strain that Symantec calls “Reedum” (note the Windows service name of the malicious process is the same as the ThreatExpert analysis –”POSWDS”). Interestingly, a search inVirustotal.com — a Google-owned malware scanning service — for the term “reedum” suggests that this malware has been used in previous intrusions dating back to at least June 2013; in the screen shot below left, we can see a notation added to that virustotal submission, “30503 POS malware from FBI”.
The source close to the Target investigation said that at the time this POS malware was installed in Target’s environment (sometime prior to Nov. 27, 2013), none of the 40-plus commercial antivirus tools used to scan malware at virustotal.com flagged the POS malware (or any related hacking tools that were used in the intrusion) as malicious. “They were customized to avoid detection and for use in specific environments,” the source said.
 That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.
That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.
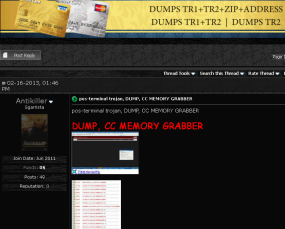
According the author of BlackPOS — an individual who uses a variety of nicknames, including “Antikiller” — the POS malware is roughly 207 kilobytes in size and is designed to bypass firewall software. The barebones “budget version” of the crimeware costs $1,800, while a more feature-rich “full version” — including options for encrypting stolen data, for example — runs $2,300.
THE ATTACK
Target has yet to honor a single request for comment from this publication, and the company has said nothing publicly about how this breach occurred. But according to sources, the attackers broke in to Target after compromising a company Web server. Somehow, the attackers were able to upload the malicious POS software to store point-of-sale machines, and then set up a control server within Target’s internal network that served as a central repository for data hoovered by all of the infected point-of-sale devices.
“The bad guys were logging in remotely to that [control server], and apparently had persistent access to it,” a source close to the investigation told KrebsOnSecurity. “They basically had to keep going in and manually collecting the dumps.”
It’s not clear what type of software powers the point-of-sale devices running at registers in Target’s U.S. stores, but multiple sources say U.S. stores have traditionally used a home-grown software called Domain Center of Excellence, which is housed on Windows XP Embeddedand Windows Embedded for Point of Service (WEPOS). Target’s Canadian stores run POS devices from Retalix, a company recently purchased by payment hardware giant NCR. According to sources, the Retalix POS systems will be rolled out to U.S. Target locations gradually at some point in the future.
WHO IS ANTIKILLER?
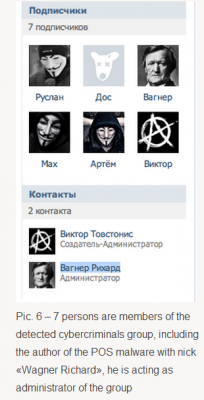
A more full-featured Breadcrumbs-level analysis of this malware author will have to wait for another day, but for now there are some clues already dug up and assembled by Russian security firm Group-IB.
Not long after Antikiller began offering his BlackPOS crimeware for sale, Group-IB published an analysis of it, stating that “customers of major US banks, such as such as Chase (Newark, Delaware), Capital One (Virginia, Richmond), Citibank (South Dakota), Union Bank of California (California, San Diego), Nordstrom FSB Debit (Scottsdale, Arizona), were compromised by this malware.”
In his sales thread on at least one crime forum, Antikiller has posted a video of his product in action. As noted by Group-IB, there is a split second in the video where one can see a URL underneath the window being recorded by the author’s screen capture software which reveals a profile at the Russian social networking site Vkontakte.ru. Group-IB goes on to link that account to a set of young Russian and Ukranian men who appear to be actively engaged in a variety of cybercrime activities, including distributed denial-of-service (DDoS) attacks and protests associated with the hackivist collective known as Anonymous.
One final note: Dozens of readers have asked whether I have more information on other retailers that were allegedly victimized along with Target in this scheme. According to Reuters, “smaller breaches on at least three other well-known U.S. retailers took place and were conducted using similar techniques as the one on Target.” Rest assured that when and if I have information about related breaches I feel confident enough about to publish, you will read about it here first.
http://krebsonsecurity.com/2014/01/a-closer-look-at-the-target-malware-part-ii/
A Closer Look at the Target Malware, Part II
Yesterday’s story about the point-of-sale malware used in the Target attack has prompted a flood of analysis and reporting from antivirus and security vendors about related malware. Buried within those reports are some interesting details that speak to possible actors involved and to the timing and discovery of this breach.
 As is the case with many data breaches, the attackers in this attack used a virtual toolbox of crimeware to get the job done. As I noted in a Tweet shortly after filing my story Wednesday, at least one of those malware samples includes the text string “Rescator.” Loyal readers of this blog will probably find this name familiar. That’s because Rescator was the subject of a blog post that I published on Dec. 24, 2013, titled “Who is Selling Cards from Target?“.
As is the case with many data breaches, the attackers in this attack used a virtual toolbox of crimeware to get the job done. As I noted in a Tweet shortly after filing my story Wednesday, at least one of those malware samples includes the text string “Rescator.” Loyal readers of this blog will probably find this name familiar. That’s because Rescator was the subject of a blog post that I published on Dec. 24, 2013, titled “Who is Selling Cards from Target?“.
In that post, I examined a network of underground cybercrime shops that were selling almost exclusively credit and debit card accounts stolen from Target stores. I showed how those underground stores all traced back to a miscreant who uses the nickname Rescator, and how clues about Rescator’s real-life identity suggested he might be a particular young man in Odessa, Ukraine.
This afternoon, McAfee published a blog post confirming many of the findings in my story yesterday, including that two malware uploaders used in connection with the Target attack contained the Rescator string:
“z:\Projects\Rescator\uploader\Debug\scheck.pdb”.
![A private message on cpro[dot]su between Rescator and a member interested in his card shop. Notice the ad for Rescator's email flood service at the bottom.](http://krebsonsecurity.com/wp-content/uploads/2013/12/rescator-pm-cpro-600x153.png)
A private message on cpro[dot]su between Rescator and a member interested in his card shop. Notice the ad for Rescator’s email flood service at the bottom.
Earlier this morning, Seculert posted an analysis that confirmed my reporting that the thieves used a central server within Target to aggregate the data hoovered up by the point-of-sale malware installed at Target. According to Seculert, the attack consisted of two stages.
“First, the malware that infected Target’s checkout counters (PoS) extracted credit numbers and sensitive personal details. Then, after staying undetected for 6 days, the malware started transmitting the stolen data to an external FTP server, using another infected machine within the Target network.”
Seculert continues: “Further analysis of the attack has revealed the following: On December 2, the malware began transmitting payloads of stolen data to a FTP server of what appears to be a hijacked website. These transmissions occurred several times a day over a 2 week period. Also on December 2, the cyber criminals behind the attack used a virtual private server (VPS) located in Russia to download the stolen data from the FTP. They continued to download the data over 2 weeks for a total of 11 GBs of stolen sensitive customer information. While none of this data remains on the FTP server today, analysis of publicly available access logs indicates that Target was the only retailer affected. So far there is no indication of any relationship to the Neiman Marcus attack.”
Target has taken quite a few lumps from critics who say the company waited too long to disclose the breach, and new details about when it may have known something was wrong are likely to fan those flames. As I wrote yesterday, the point-of-sale malware used in Target referenced a domain within Target’s infrastructure called “ttcopscli3acs”. Several sources, including Seculert’s Aviv Raff and Dmitri Alperovitch at CrowdStrike, searched for other files with that unique string within the corpus of malware uploaded to Virustotal.com, a service that employs more than 40 commercial antivirus tools to produce reports about suspicious files submitted by users.
That search turned up numerous related files — including the aforementioned malware uploaders with Rescator’s nickname inside — all dated Dec. 11, 2013. Since this malware is widely thought to have been custom-made specifically for the Target intrusion, it stands to reason that someone within Target (or a security contractor working at the company’s behest) first detected the malware used in the breach on that date, and then submitted it to Virustotal.
Yesterday’s story cited sources saying the malware used in the Target breach was carefully crafted to avoid detection by all antivirus tools on the market. These two virustotal scan results from Jan. 16 (today) show that even to this day not a single antivirus product on the market detects these two malicious files used in the Target attack. Granted, the antivirus tools used at virustotal.com do not include behavioral detection (testing mostly for known threat signatures). I point it out mainly because nobody else has so far.
Incidentally, in malware-writer parlance, the practice of obfuscating malware so that it is no longer detected by commercial antivirus tools is known as making the malware “Fully Un-Detectable,” or “FUD” as most denizens of cybercrime forums call it. This is a somewhat amusing acronym to describe the state of a thing that is often used by security industry marketing people to generate a great deal of real-world FUD, a.k.a. Fear Uncertainty and Doubt.